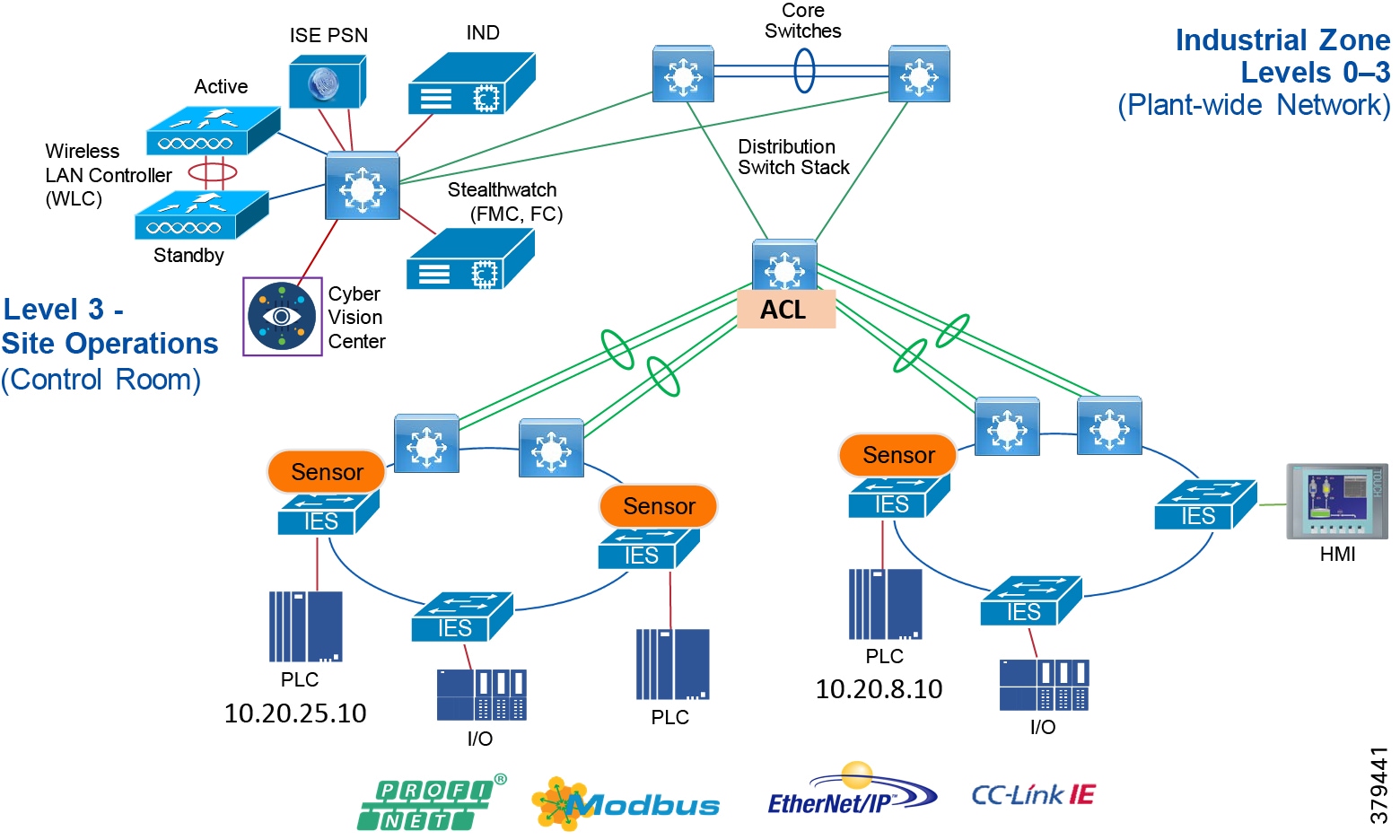
The FAQ addresses common questions in terms of features, usage, as well as support related topics. All sections link to corresponding articles. For detailed documentation use the search bar or write a ticket to support@anydesk.com. Show/hide all answers. . Workstations A and B will be able to Telnet to each other. All other traffic will be denied. The ACL will have no effect because it should be applied in the outbound direction on the FastEthernet interfaces. The ACL will deny all traffic because of the implied deny ip any any statement at the end of the ACL.
This is the Linux content page of the CL Wiki Service Desk Knowledgebase. Its purpose is to provide information to the Service Desk team on how to handle problems and requests about this CL service. If you are involved with the provision of this CL service please feel free to add to the knowledge about that it.
If CL staff need to tell the Service Desk team about problems with this service please email
sys-admin-aside@cl.cam.ac.uk.
Return to the Service Desk Knowledgebase SERVICE PORTFOLIO
Key Service Description & URLs
- Computer Laboratory News (Twitter use @UC_CL_SysAdm)
CL Customer Documentation
Further CL Sys-Admin Resources
- http://www.wiki.cl.cam.ac.uk/clwiki/SysInfo/HelpDesk/Linux - Linux
- http://www.wiki.cl.cam.ac.uk/clwiki/SysInfo/MachineSetup - Full Machine Setup (for reference)
- http://www.wiki.cl.cam.ac.uk/clwiki/SysInfo/HelpDesk/LinuxSoftware - Adding software packages
Desk Rt Acl Denied Claim
Underpinning Services
- ??? - Any supporting or underpinning services
Customer-base for this Service
- Linux boxes are available to all staff and post-graduates, and well as some on the Part III Under-graduates.

Costs
- Hardware is charged for if you are a Research Assistant or a University Teaching Officer, but free to Post-graduates.
- Support is free.
SLA
- ??? - Timeframes or service level agreement for fulfilling the service
Service Desk Call Handling Procedure
- RT tickets can be escalated to the unix-admin by changing the Queue to unix-admin with the Owner set to Nobody & Status set to new. Tell the requestor:
I am passing this request over to our Unix Admin team who, I'm sure, will be in contact shortly.
'It gave an error' or 'It failed to work'
Piete Brooks (20 Feb 2015)
If someone says something like 'It gave an error' or 'It failed to work' on a Linux system please email them the following:
Dear ???,
Could you please send us a copy & paste of the command that you ran and the output that it generated? Also, would you please run the commands:
groups
sudo -l
and copy & paste the output of those into the same reply to this email.
Many thanks,
???
Removing a broken install
Vince Woodley (17 Feb 2015)
ssh to the machine in question then...
1) Find the process responsible for the lock with sudo lsof /var/lib/dpkg/lock
2) Check for running dpkg processes with something like ps -ef | grep dpkg
3) Ask the requestor if they'd like you to kill it:
I suspect I could do that by killing the rogue process -- shall I have a go?
4) Kill any dpkg processes shown above with sudo kill 1234 etc...
If they refuse to die try sudo kill -HUG 1234
5) Check each is dead with the same command again sudo kill 1234 (hopefully there will be no such process)
6) Find the exact name of the dropbox package with dpkg -l *dropb* (or similar)
7) Remove it with cl-asuser apt-get remove nautilus-dropbox
(or similar)If that fails with:-
'dpkg was interrupted, you must manually run 'sudo dpkg --configure -a' to correct'then cd /var/lib/dpkg/updates and delete all the files there with rm *
8) Do an update of the system with cl-update-system
9) Check the output to make sure that everything's okay repeating cl-update-system if necessary
Clock slew problem
Graham Titmus (3 Feb 2015)
First check if this is a physical machine or a VM. If a physical machine login to it. If a Xen VM then login to it and check if it is tied to the dom0 clock.
If that returns an error then proceed as for a standalone machine. If it returns 0 then you need to find the dom0 which hosts the VM, to find that do
When logged in to the appropriate machine (using ssh or in the case of Xen you could also connect via the Xen Centre guy) first check if it is working correctly
which should not look like this
but have multiple lines each to a remote ntp server.
If it does look like above then restart the ntpd service
and check the output again which should now look like
Linux user can't login using graphical interface
Graham Titmus (13 Jan 2015)
Symptoms: Linux user can't login using graphical interface, they enter username and password and get a blank screen then back to login
A common cause of this is a failure to access the home directory stored on the File Server (AKA Elmer or Filer), X (the window manager) needs to write a file there when it starts the user session.To diagnose if this is the problem do the following:-
- Remote login to the machine using ssh -K hostname@cl.cam.ac.uk from a CL machine - check if your home directory is present (ls -al ~). If it is look to see if the users home directory is present (ls -al ~crsid).
- If the home directory is missing then try to restart the auto mounter (cl-asuser service autofs restart).
- Look at the mounted filesystems (grep ldap /proc/mounts - will show which systems have been auto mounted using data form the LDAP).
An alternative is to ask the user to check if it is the machine failing to log them in or a problem with X by getting them to try on the text console (Select with Ctrl-Alt-F2).If they can login there but have no home then it is probably a problem with the filesystem. If they cannot login at all then it is an authentication problem. They should then try from another machine that is known to work to check their login works.
Adding privileged or 'assigned' users
Linux PCs Assigned to Users:
Machines are setup with a single 'assigned user' having both cl-asuser access (due to owning the file /etc/user-config/bundles) and sudo access (due to being in a suitable group which has sudo rights). If the assigned user has not been setup (because a machine has been moved to a new user or was not done when the machine was installed):
- Login to the user's machine from a Lab machine such as slogin-serv using ssh -K $MachineName
- First run cl-asuser cl-hostid-fix --user $CRSid which will show you what it thinks needs to be done and (if it looks okay)
- Then run cl-asuser cl-hostid-fix --user $CRSid -a to actually do it.
- The user should be told that if they are currently logged in they must logout & log back in again for the changes to take effect.
- Then [Edit] & [Update] the machine names' entry(s) in the inventory and set the User: $CRSid and a Comment like RT#12345 User=$CRSid.
NOTE: If the user's account and home directory have not already been created (as in Create home directories for new users) you will get errors like:
and you will need to re-run the command after the account has been created.
Group Servers & PCs with multiple admins:
For group servers which may want multiple admins, they can use being in the sudo group to grant privileges to other users. Liaise with the machine owner to check what is wanted. To actually do it:
First ssh -K $hostname (if it's not turned on try cl-boot-mc $MachineName on any of the slogin machines, or Wake-on-Lan (WoL) - wait 3-4 minutes for it to appear online) and then...
cl-asuser access: (if ACLs are enabled) is setup using sudo setfacl -m u:$CRSid:rw /etc/user-config/bundles where $CRSid should be replaced by the CRSid of the person who is to be granted privilege. cl-asuser privileges should then be available immediately.
sudo access: is setup by using an editor to add them to the relevant group (e.g. sudo or root) in the file /etc/group. To do this ssh -K $hostname and then:
- sudo vi /etc/group
- [sudo] password for abc123: enter your CL password
- Add the user's CRSid to the line like sudo:x:27:localadmin,sg692 by scrolling down to it with the arrow-keys and using [Shift]+A to enter --- INSERT --- mode and typing in ,$CRSid
- [ESC] out of insert mode
- Write and quit with :wg and [Enter]
(Note that sudo privileges will only take effect in new sessions.)
If there are sudo problems use groups $CRSid to check which groups the user is in, and sudo -l -U $CRSid to check the status. Check /etc/sudoers using sudo view sudoers and /etc/sudoers.d/* to check which groups give ALL access.
Removing privileged or 'assigned' users when they leave
When the assigned user leaves the machine is usually removed from the network and into GC20.As it will be re-installed when re-allocated there is no need to un-assign the user.If it was needed to be done for some reason it could always be assigned to 'localadmin'
If the person leaving had been granted 'assigned user' type privileges on someone else's machine (which was remaining un-reclaimed on the network) then the leaving person could have their access undone with:
- delete user from /etc/groups
- remove from ACL with: sudo setfacl -x u:$CRSid /etc/user-config/bundles
(4.7) BMC ACL - when up if present
Based on http://www.wiki.cl.cam.ac.uk/clwiki/SysInfo/MachineSetup#bmcaclPiete Brooks (23 Feb 2015)
- Use an omnipotent machine (laira toton or radyr) e.g. ssh -K laira (or toton) & press [Enter] to get the laira:~$ prompt
- Replacing $CRSid with the assigned user's CRSid in the following instructions use cd /home/$CRSid/ and [Enter]
- Check if the files .amtpw, .amtuser, .ipmi-pw & .ipmi-user already exist by running the command to create them - if they already exist, it will list the files:
/usr/groups/netmaint/setamt $CRSid - Display the 'random' password for later use, e.g. for iAMT
sudo cat /home/$CRSid/.amtpw - Use a Windows Remote Desktop Connection to a machine on the Computer Lab network such as the Terminal Server ts01.ad.cl.cam.ac.uk
- On the server, open a web-browser to the appropriate BMC interface URL i.e.:
- For a workstation called $host - IAMT BMC: http://$host-bmc.cl.cam.ac.uk:16992
- For WPCM450 on a server called $host - IPMI BMC: http://$host.bmc.cl.cam.ac.uk
- [Login] as admin with the special admin password
- Go to User Accounts
- First select any previous assigned user's CRSid and then [Remove] & [Remove]
- Click [New] and enter the User name:$CRSid then the new random 8 character password created above in step 8 twice and select Administrator: Grant access to all pages then [Submit]Be careful when setting the P/W to ensure you do it for the USER and rather than Admin - if you do then try go back to laira and do:
to Display the 'random' password (take care not to include the password if reporting what happened using cut&paste)
- You can't logout of the BMC interface so just [X] close the web-browser and Log Off the server.
- On laira, for an iAMT BMC, test it was done correctly. The command below should not generate any 'failed' warnings:
NOTE: We do not normally expect the user to have to explicitly use the credentials - they are normally used by commands such as:
- cl-boot-mc - which boots a machine using the BMC
- ipmitool - which does raw commands to an IPMI BMC
- cl-amttool - which does raw commands to an IAMT BMC
- amtterm - which connects to the serial console of an IAMT WS
4.9 WoL - at leisure
- See http://www.wiki.cl.cam.ac.uk/clwiki/SysInfo/MachineSetup#head-9d3248bbd29dbd4b4a5fa47d29346972f76fff4f
Local Disk Full
First check if sufficient space can be obtained by clearing out old files
if that does not give adequate space thennormally just Enlarge the FS using
If there isn't enough free space to easily enlarge the partition (physical too small; RAID using all of the component partitions; VG full for LVM), the partition needs to be enlarged pass the ticket on to the Backoffice queue.
Linux Operating System Upgrades
- See Linux Operating System Upgrades
Requests to Install Linux Packages
If an extra package is wanted on a Linux machine, the manager (i.e. 'Assigned User') should be asked to add it. To determine the assigned user, see the User field of the machine in the Inventory Database, or see who has write access to /etc/user-config/bundles e.g. using getfacl /etc/user-config/bundles, the file which lists the packages which should automatically be added, which is copied over when a machine is reinstalled. Normally it is one user and the sysadmin group, but ACLs may be used to add other users or groups (e.g. the srg-tsars unix group in the Group Server example below).
After checking with the appropriate person if permission is agreed then to grant a user the ability to add packages do
and then inform the user that they can now install packages by adding them to /etc/user-config/bundles and running
or can manually check each package before adding it using
or tell them that the request has been denied if the authorised person says no.
Classes of Machine Management
1) User Workstations:
- These are 'tower' systems;
- They are in a user's office;
- The 'Assigned User' in the Inventory is the owner, or SSH to the workstation and use getfacl /etc/user-config/bundles to reveal the owner's CRSid;
- There is normally only one user so refer the request to them.
- For example:
2) Group Servers:
- These are rack mount or virtual machines;
- They are in a machine room (GN09, SE18 & FN11);
- They are owned by a UTO;
- The 'Assigned User' in the Inventory is the owner, or SSH to the server and use getfacl /etc/user-config/bundles to reveal the owner's CRSid;
- The owner is normally the 'assigned manager' so that one person has an overview so refer the request to them.
- For example:
3) Departmental MPhil Pool:
- These are 'tower' systems;
- They are in a teaching Lab (SW02 & SW11);
- They have systematic names, e.g. acs-34;
- They are owned by a Computer Lab CO (pb22, gt19, maj1, ckh11), 'Lab' or some such;
- The 'Assigned User' in the Inventory is the owner (workstations not accessible via ssh);
- Whilst individual users can load private copies of any 'special' things they need in their $HOME (and maybe setting some environment variables to find it); anything of use to the bulk of the people doing the course should be requested by the course giver.
- Escalate so the Computer Lab COs can decide if the case is strong enough to install it on all pool machines.
4) Departmental Servers:
- These are rack mount or Virtual machines;
- They are in a machine room (GN09, SE18 & FN11);
- They are owned by a Computer Lab CO (pb22, gt19, maj1, ckh11), 'Lab' or some such;
- The 'Assigned User' in the Inventory is the owner, or SSH to the server and use getfacl /etc/user-config/bundles to reveal the owner as 'localadmin', or some such;
- Escalate so the Computer Lab COs can decide if the case is strong enough and where to install it.
- For example:
Contacts
Primary
- unix-admin RT queue
Other
Availability
- Monday: 09:00-17:00
- Tuesday: 09:00-17:00
- Wednesday: 09:00-17:00
- Thursday: 09:00-17:00
- Friday: 09:00-17:00
- Saturday: Closed
- Sunday: Closed
Hints, Tips & Known Issues
If the SysAdmin Team Can't SSH into a Linux machine
Piete Brooks (03/06/15)
If you have problems logging in to Linux machine called $hostname e.g.:
connect to an omnipotent machine (e.g. laira) and use:
sudo ssh $hostname
This works for:

- stand-alone machines with very limited number of users
- machines on which Kerberos is failing, so can't auth the user
- machines on which LDAP is failing, so can't set groups etc
- machines on which DNS is failing, so can't check caller's DNS name etc.
Finding out a machine's operating system
Graham Titmus (26/05/15)
Whilst it's only the best guess you can try logging into laira and running the command:
cl-hosts -p MachineName
to find out what operating system a machine is believed to have.
The 'stty: standard input: inappropriate ioctl for device' error
Piete Brooks (20/03/15)
The 'inappropriate ioctl for device' error is probably when the .profile uses the stty command to set your erase, kill, and interrupt characters e.g.:
To fix this error: you could comment out the use of stty in your .profile file using '# ' at the start of each line above, or even chose to rename the .profile file as old_profile using the command: mv .profile old_profile
Waking Up a Lab Computer which has BMC
Piete Brooks (20/03/15)
First give a reboot a try with Wake-on-Lan (WoL) a try (and wait 3-4 minutes for it to appear online) but it's a highly unreliable protocol. It sends a packet into the ether and hopes it arrives - there is no ACK. In order to work, the client needs to have set everything up perfectly. A much better method for the 'assigned user' is to login to an slogin-serv machine and first run:
ping MachineName-bmc
and within (say) 10 seconds the BMC should be responsive. If that fails try running:
ping MachineName.bmc
(Servers tend to have a dedicated connection for the BMC, which is on the 'BMC VLAN', which has its own subnet and domain .bmc) Then run:
cl-boot-mc MachineName
which will use a much more helpful mechanism. If the machine is already awake you will see something like:
(You may need to hit Ctrl+C to end the process if the machine is actually asleep.)
Categorising Keywords
- Linux Ubuntu PC Person Computer
This article helps fix an issue where you can't start a Microsoft Store App if the default registry or file permissions is modified.
Applies to: Windows 10 - all editions
Original KB number: 2798317
Note
This article is intended for IT professionals. For home users who encounter Microsoft Store App issues, go to Fix problems with apps from Microsoft Store.
Issue 1
When you select a Microsoft Store App, the App begins to start, and then Windows just returns to the start screen. No on-screen error is displayed.
Microsoft-Windows-Immersive-Shell event 5961 is logged under the Applications and Services LogsMicrosoftWindowsAppsMicrosoft-Windows-TWinUI/Operational event log path:
Note
The app portion of the example event, <app name>, will change depending on the application that fails to start.
Possible values for <app name> include but aren't limited to:
microsoft.windowscommunicationsapps_8wekyb3d8bbwe!Microsoft.WindowsLive.Chat
Prefixes for other built-in Microsoft Store Apps include:
Microsoft.BingFinance_8wekyb3d8bbwe!<app identifier>
Microsoft.BingMaps_8wekyb3d8bbwe!<app identifier>
Microsoft.BingNews_8wekyb3d8bbwe!<app identifier>
Microsoft.BingSports_8wekyb3d8bbwe!<app identifier>
Microsoft.BingTravel_8wekyb3d8bbwe!<app identifier>
Microsoft.BingWeather_8wekyb3d8bbwe!<app identifier>
Microsoft.Bing_8wekyb3d8bbwe!<app identifier>
Microsoft.Camera_8wekyb3d8bbwe!<app identifier>
Microsoft.Media.PlayReadyClient_8wekyb3d8bbwe!<app identifier>
microsoft.microsoftskydrive_8wekyb3d8bbwe!<app identifier>
Microsoft.Reader_8wekyb3d8bbwe!<app identifier>
Microsoft.VCLibs.110.00_8wekyb3d8bbwe!<app identifier>
microsoft.windows.authhost.a_8wekyb3d8bbwe!<app identifier>
microsoft.windowscommunicationsapps_8wekyb3d8bbwe!<app identifier>
microsoft.windowsphotos_8wekyb3d8bbwe!<app identifier>
Microsoft.WinJS.1.0.RC_8wekyb3d8bbwe!<app identifier>
Microsoft.WinJS.1.0_8wekyb3d8bbwe!<app identifier>
Microsoft.XboxLIVEGames_8wekyb3d8bbwe!<app identifier>
Microsoft.ZuneMusic_8wekyb3d8bbwe!<app identifier>
Microsoft.ZuneVideo_8wekyb3d8bbwe!<app identifier>
Issue 2
You can't start a Microsoft Store App, open Start screen, and use Search in Windows. Additionally, you receive the following event log in Application logs:
If you use Process Monitor to track the Apps' executable or related files, you may see access denied is logged. It points to the missing permissions for the current logon user. It includes:
Registry hives and its subkeys:
- HKEY_CLASSES_ROOT
- HKEY_LOCAL_MACHINEDrivers
- HKEY_LOCAL_MACHINEHARDWARE
- HKEY_LOCAL_MACHINESAM
- HKEY_LOCAL_MACHINESOFTWARE
- HKEY_LOCAL_MACHINESYSTEM
- HKEY_USERS
For file subsystem:
- Program Files - Read, Read and Execute, and List folder Contents
- Windows - Read, Read and Execute, and List folder Contents
- Users<userName>AppDataLocalMicrosoftWindowsWER - Special Permissions (List folder/read data, and Create Folders/Append Data)
Cause for issue 1
Registry and or file system permissions may have been changed from their defaults.
The All Application Packages group is a well-known group with a predefined SID. The group must have specific access to certain locations of the registry and file system for Microsoft Store Apps to function properly.
Cause for issue 2
This issue occurs because the read permission is missing from any or all the keys. In this case, 0xc000027b is logged. This error without exception is missing permission for ALL APPLICATION PACKAGES at registry location or file subsystem locations.
Registry and file system permission must be reverted to a state that will allow Microsoft Store App to function
Note
Only change the permission of the registry keys that are known to cause the access denied error. Incorrectly changing registry keys' permission might cause serious problems or unintentionally weaken security settings.
Extensive permission changes that are propagated throughout the registry and file system cannot be undone. Microsoft will provide commercially reasonable efforts in line with your support contract. However, you cannot currently roll back these changes. We can guarantee only that you can return to the recommended out-of-the-box settings by reformatting the hard disk drive and by reinstalling the operating system.
If you use Group Policy to manage permissions, or if you're unsure whether Group Policy is used to manage permissions, follow these steps:
- Unjoin the computer from the domain or put the computer in a test OU with block policy inheritance enabled. This action prevents the domain-based Group Policy from reapplying the permission changes and breaking the modern applications again after you've fixed them.
- Add permissions where they're required per the following details.
- Edit the Group Policy that manages to permissions so that it no longer breaks modern application.
Registry and File System permission must be reverted back to a state that will allow Microsoft Store App to function. Follow this method to resolve the issue:
- Determine if file system permissions have been changed. If not, see the More information section below.
- If so, how were they changed? Manually or with Group Policy?
- Determine if registry permissions have been changed If not, see the More information section below.
- If so, how were they changed? Manually or with Group Policy?
- Verify secpol and GPPs specifically.
Determine if file system permissions have been changed
Check the folders listed below. Determine if the All Application Packages group has the access indicated. Most but not all sub directories of Windows, Program Files, and WER also grant permissions to the All Application Packages group.
- Program Files - Read, Read and Execute, and List folder Contents
- Windows - Read, Read and Execute, and List folder Contents
- Users<userName>AppDataLocalMicrosoftWindowsWER - Special Permissions (List folder/read data, and Create Folders/Append Data)
Determine if registry permissions have changed
Check the registry keys listed below. Make sure the All Applications Packages group has the Read permissions to the following registry paths:
- HKEY_CLASSES_ROOT
- HKEY_LOCAL_MACHINEDrivers
- HKEY_LOCAL_MACHINEHARDWARE
- HKEY_LOCAL_MACHINESAM
- HKEY_LOCAL_MACHINESOFTWARE
- HKEY_LOCAL_MACHINESYSTEM
- HKEY_USERS
Most but not all of the subkeys of the registry keys listed above will grant the All Application Packages group read access.
Determine if Group Policy is being used to manage permissions
Sign in to a PC as a user experiencing the problem.
Open an administrative command prompt then run the following command:
Open the file gpreport.html and expand the following path:
Computer Settings > PoliciesWindows SettingsSecurity Settings. Look for File System and Registry. If these exist, then GP is assigning permission. You must edit the GP to include the necessary permissions for the All Application Packages group.
Steps to fix the problem
Depending on how the file system permissions were changed will determine how to recover from the problem. The most common ways permissions are changed manually and by Group Policy.
Important
Make sure that you test your resolution in a lab before widely deploying. Always backup any important data before changing registry and file system permissions.
Fix file system permissions that's changed manually
- Open File Explorer.
- Browse to c:Program Files.
- Right click and select properties.
- Select the Security tab.
- Select the Advanced button.
- Select the Change permissions button.
- Select the Add button.
- Select the Select a principal link.
- Select the locations button and select the local computer.
- Add the All Applications Packages group name and select ok.
- Make sure that Type = allow and Applies to = This folder, subfolder, and files.
- Check Read & Execute, List folder contents, and Read.
- Check the Replace all child object permissions with inheritable permission entries from this object checkbox.
- Select Apply and OK.
- Repeat for c:Windows.
- Repeat for c:Users but grant the All Application Packages group Full Control.
- Select Apply and OK.
Fix file system permissions that's changed by Group Policy
Have a Group Policy administrator do the following steps:
Desk Rt Acl Denied Symptoms
- Open Group Policy Administrative Console.
- Locate the GPO identified in the step Determine if Group Policy is being used to manage permissions.
- Right-click and select edit.
- Go to the location Computer
ConfigurationPolicyWindows SettingsSecurity SettingsFile System. - If there's an entry for the paths already created, you can edit it. If no entry exists, create a new entry for each path.
- To create a new entry, right-click file system and select add file.
- Browse to the path c:Program Files, select OK.
- Select the Add button.
- Select the locations button and select the local machine name.
- Add the All Application Packages group and grant them the Read, Read and Execute, and List folder Contents permissions.
- Select Apply and OK.
- Select the Replace existing permissions on all subfolders and files with inheritable permissions option.
- Repeat for C:Windows.
- Repeat for C:Users, however, grant the All Application Packages group Full Control.
You'll need to wait for the Group policy change to replicate to all Domain Controllers and for all clients to update their Group Policy settings.
Note
Processing the File System changes will incur some logon delay the first time this policy is processed. Subsequent logons will not be impacted unless changes are made to the policy. As an alternative you can use a script that is called post logon by the user is run as a scheduled task.
Fix registry permissions that's changed manually
- Open regedit.exe.
- Right click on HKEY_Users and select properties.
- Make sure that All Application Packages has Read.
- Repeat for HKEY_CLASSES_ROOT.
- Expand HKEY_LOCAL_MACHINE. Check the subkeys HARDWARE, SAM, SOFTWARE, SYSTEM. Make sure that All Application Packages has the Read permission.
Fix Registry Permissions that's changed by Group Policy
Have a Group Policy administrator do the following steps:
- Open Group Policy Administrative Console.
- Locate the GPO identified in the step Determine if Group Policy is being used to manage permissions.
- Right-click and select edit.
- Go to the location Computer
ConfigurationPolicyWindows SettingsSecurity SettingsRegistry. - Right Click and select Add Key.
- Select CLASSES_ROOT.
- Select the Add button.
- Select the locations button and select the local machine name.
- Add the All Application Packages group and grant them Read.
- Repeat for Users.
- Repeat for MACHINEHARDWARE, MACHINESAM, MACHINESOFTWARE, and MACHINESYSTEM.
More information
For more information, see Microsoft Store Apps Fail to Start if the User Profiles or the ProgramData directory are Moved from their Default Location.
File system and registry access control list modifications
Windows XP and later versions of Windows have tightened permissions throughout the system. So extensive changes to default permissions shouldn't be necessary.
Extra discretionary access control list (DACL) changes may invalidate all or most of the application compatibility testing done by Microsoft. Frequently, changes such as these haven't undergone the thorough testing that Microsoft has done on other settings. Support cases and field experience have shown that DACL edits change the fundamental behavior of the operating system, frequently in unintended ways. These changes affect application compatibility and stability and reduce functionality, about both performance and capability.
Anydesk The Session Has Ended Desk_rt_acl_denied
Because of these changes, we don't recommend you modify file system DACLs on files that are included with the operating system on production systems. We recommend you evaluate any other ACL changes against a known threat to understand any potential advantages that the changes may lend to a specific configuration. For these reasons, our guides make only minimal DACL changes and only to Windows 2000. For Windows 2000, several minor changes are required. These changes are described in the Windows 2000 Security Hardening Guide.
Extensive permission changes propagated throughout the registry and file system can't be undone. New folders, such as user profile folders that weren't present at the original installation of the operating system, may be affected. So you can't roll back the original DACLs if you:
- remove a Group Policy setting that performs DACL changes
- apply the system defaults
Changes to the DACL in the %SystemDrive% folder may cause the following scenarios:
- The Recycle Bin no longer functions as designed, and files cannot be recovered.
- A reduction of security that lets a non-administrator view the contents of the administrator's Recycle Bin.
- The failure of user profiles to function as expected.
- A reduction of security that provides interactive users with read access to some or to all user profiles on the system.
- Performance problems when many DACL edits are loaded into a Group Policy object that includes long logon times or repeated restarts of the target system.
- Performance problems, including system slowdowns, every 16 hours or so as Group Policy settings are reapplied.
- Application compatibility problems or application crashes.
To help you remove the worst results of such file and registry permissions, Microsoft will provide commercially reasonable efforts in line with your support contract. However, you can't currently roll back these changes. We can guarantee only that you can return to the recommended out-of-the-box settings by reformatting the hard disk drive and by reinstalling the operating system.
For example, modifications to registry DACLs affect large parts of the registry hives and may cause systems to no longer function as expected. Modifying the DACLs on single registry keys poses less of a problem to many systems. We recommend you carefully consider and test these changes before you implement them. And we can guarantee only that you can return to the recommended out-of-the-box settings if you reformat and reinstall the operating system.
Comments are closed.